Secure Access
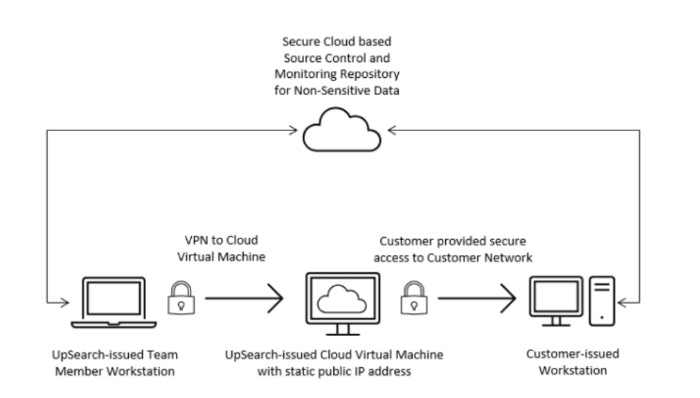
Clients must provide UpSearch with secure 24×7 access to its environment. Virtual Private Network (VPN) is the most common type of secure access clients grant. UpSearch technical team members will configure security mechanisms required to implement clients’ specified connectivity protocols. Once connected to the client’s environment, UpSearch team members use remote desktop protocol (RDP), or other client provided remote access methods to connect to the client-specified jump box.
UpSearch team members are not permitted to transfer/remove/migrate Sensitive Data (Personal Data or Demographic Data) from the client-controlled environment.
Client Non-Sensitive Data may be stored in UpSearch’s secure environment. UpSearch defines Non-Sensitive Data as any information relating to aggregate or meta information that does not relate to a natural identifiable entity. Examples of Non-Sensitive data includes, without limitation,
• Assessment and event results, such as disk space, index analysis, query plans that do not contain
sensitive data, and infrastructure catalog views
• Global and unique server identifiers and performance and/or configuration metrics
• Trace analysis files that do not contain sensitive data
Support Workstation
Client must provide UpSearch with a dedicated workstation to use within its environment that conforms to the following specifications:
• On-Premise:
o 4 vCPU, 16GB RAM, 10GB network connection.
o If the monitoring database is installed on the workstation, additional storage may be required.
o 150 GB of Storage (Excluding the C: drive) may be required to store trace results.
o Minimum Operating System: Windows 10 Pro or Windows Server 2019 Standard (Note: the Windows version should be the same version or later of your latest version of Windows deployed in your environment)
• Cloud:
o Azure A4/D4 or equivalent in AWS
o Operating System: Windows Server 2019 Datacenter Edition latest image
• UpSearch will install SQL Server Developer Edition, appropriate PowerShell modules, and any other required software. A list of standard tools will be provided upon request.
• Client can leverage and whitelist UpSearch’s Public Static IP address (20.228.197.51) to limit and control access to their environment.
Security Requirements
Clients can create Active Directory Groups for our AD accounts or leverage existing groups to make permissions management easier. Full administrative privileges in both Windows and SQL Server for any server that UpSearch will administer are required.
Client will create the following accounts:
• An interactive log-on account for each UpSearch team member with minimal domain permissions, local administrative access to the Windows OS and granted the sysadmin server role for SQL Server, for any server to be administered by UpSearch.
• A monitoring account with local administrative access to the Windows OS and granted the sysadmin server role for SQL Server, for any server monitored by UpSearch.
• A service account that UpSearch will use to set up unattended processes with the same permissions as the monitoring account. This account will run PowerShell scripts or other automated processes against client’s data platform environment.
• In many cases, clients will provide a single account to be used in place of the monitoring and service accounts in addition to the dedicated AD account for each UpSearch team member.
Source Control
Any T-SQL or PowerShell code developed for a client must be stored in source control. UpSearch will provide a code repository in GitHub, and all code related to that client will be stored there. A clone of the repository will be on the client workstation.

